-
Bug
-
Resolution: Unresolved
-
Major
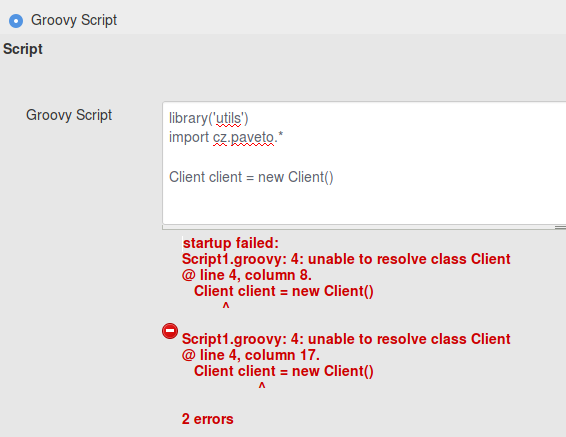
In groovy script in parameter i havent access into Groovy shared library.
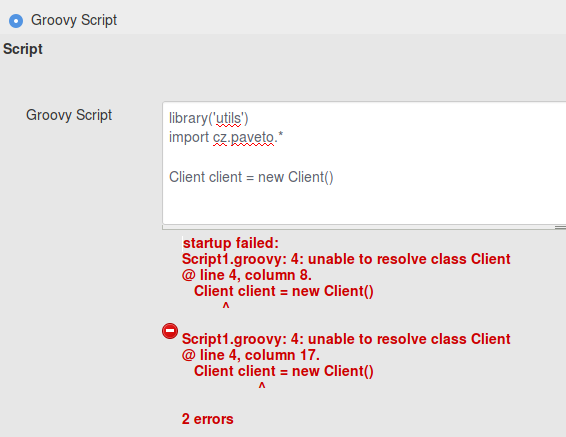
I use version 1.5.3 of Active Choices Plugin.
In job workflow works same include.
In groovy script in parameter i havent access into Groovy shared library.
I use version 1.5.3 of Active Choices Plugin.
In job workflow works same include.