-
Bug
-
Resolution: Unresolved
-
Critical
-
None
-
Jenkins ver. 2.176.2
Note: setting to Critical as this exposes serious security issues.
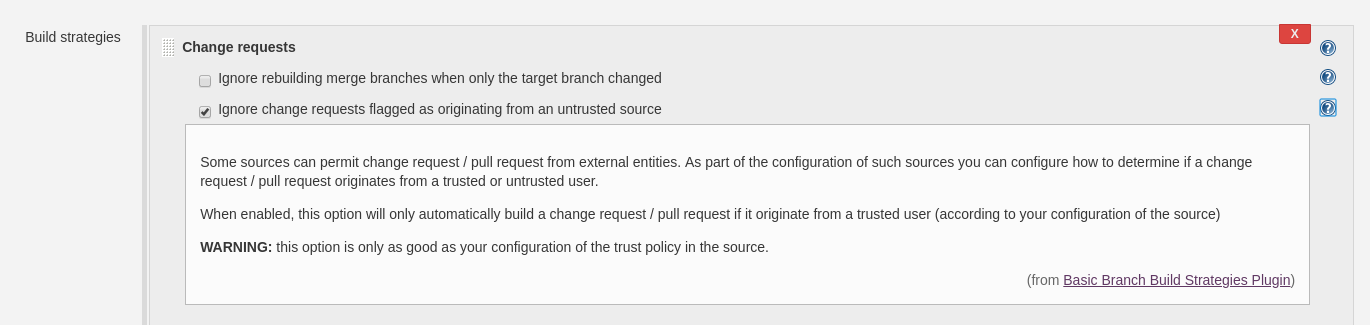
The Ignore change requests flagged as originating from an untrusted source build strategy:
seems to only work on the first commit to a PR from an untrusted source. If a somebody with the appropriate permissions executes a Build Now on that PR, presumably because they have done a code inspection looking for nefarious use of the build and test resources, any subsequent pushes to that PR, even from untrusted sources will get automatically built, without the need for somebody to again go execute a Build Now.
This of course means that such a PR could introduce nefarious use, without review, after having it's first commit in the PR approved and built.
Every new commit to a PR from an untrusted source needs to be prevented from building until somebody approves it with an explicit Build Now click. Otherwise this whole option becomes much less useful.
