-
Bug
-
Resolution: Unresolved
-
Minor
-
None
-
Jenkins 2.222.1
OpenJDK 11.0.6+10-post-Ubuntu-1ubuntu118.04.1
Ubuntu 18.04 LTS
ldap plugin version 1.21
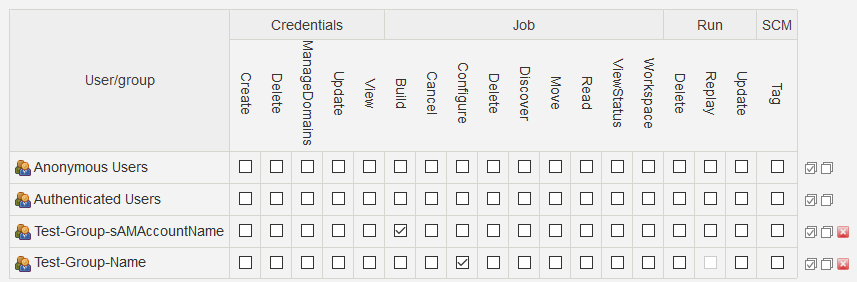
Project-based Matrix Authorization Strategy
Groups entered by samaccountname are not giving any permissions to its members. Group looks like is correctly recognized.
Groups entered by cn/name are working correct.
Configuration details:
User search filter: (& (objectCategory=Person)(objectclass=user)(samaccountname={0})(!(userAccountControl:1.2.840.113556.1.4.803:=2)) )
Group search filter: (& (objectclass=group) (| (samaccountname={0})(cn={0}) ) )
Group membership|Search for LDAP groups containing user|Group membership filter: (member={0})
Example: Member of below group will have only 'Configure' permissions.